WLS 3.7.22 is here! The latest version of SIEM, format, and protocol agnostic Windows event log forwarding with process creation metadata and user defined contextual information, now with LNK parsing, file system minifilter reporting, WBCL reporting, and sysmon configuration management!
CommandMonitor
- Added support for Windows 11 command history when cmd.exe is launched inside Windows Terminal
FileData
- Added LNK parsing and reporting
- Processes launched from a shortcut, when the LNK field is requested, will have LNK details logged along with user-defined metadata
2022-09-26T12:07:18-05:00 host WLS_FileData: LogType=”WLS”, AccessTime=”2/23/2022 3:51:57 PM”, BaseFileName=”Configuration Manager Console.lnk”, CreationTime=”7/27/2021 2:33:52 AM”, CreationTime1=”2/23/2022 9:51:59 AM”, FileAttributes=”ARCHIVE”, FileDataName=”LNK”, FileName=”C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Microsoft Endpoint Manager\Configuration Manager\Configuration Manager Console.lnk”, HotKey=””, IconIndex=”0″, KnownFolder=”7c5a40ef-a0fb-4bfc-874a-c0f2e0b9fa8e”, LastAccessTime=”9/26/2022 12:06:41 PM”, LastWriteTime=”2/23/2022 9:51:59 AM”, Length=”1409″, LinkFlags=”HasLinkTargetIDList, HasLinkInfo, HasRelativePath, IsUnicode”, LinkInfoFlags=”VolumeIDAndLocalBasePath”, LocalBasePath=”C:\Program Files (x86)\Microsoft Endpoint Manager\AdminConsole\bin\Microsoft.ConfigurationManagement.exe”, MacAddress=”F80DAC6E57E8″, MachineID=”host”, MD5=”D82ABC2B24AA63332BE73F80656AD31D”, PropertyStoreCount=”2″, RelativePath=”..\..\..\..\..\..\..\Program Files (x86)\Microsoft Endpoint Manager\AdminConsole\bin\Microsoft.ConfigurationManagement.exe”, SHA1=”08F381B34236F9F12F62FEE6FF88B96D5B6DAEE0″, ShowCommand=”1″, SID=”S-1-5-18″, Size=”434544″, SpecialFolder=”ProgramFilesX86″, User=”NT AUTHORITY\SYSTEM”, VolumeLabel=”Windows”, WLSKey=”11169″, WriteTime=”7/27/2021 2:33:52 AM”
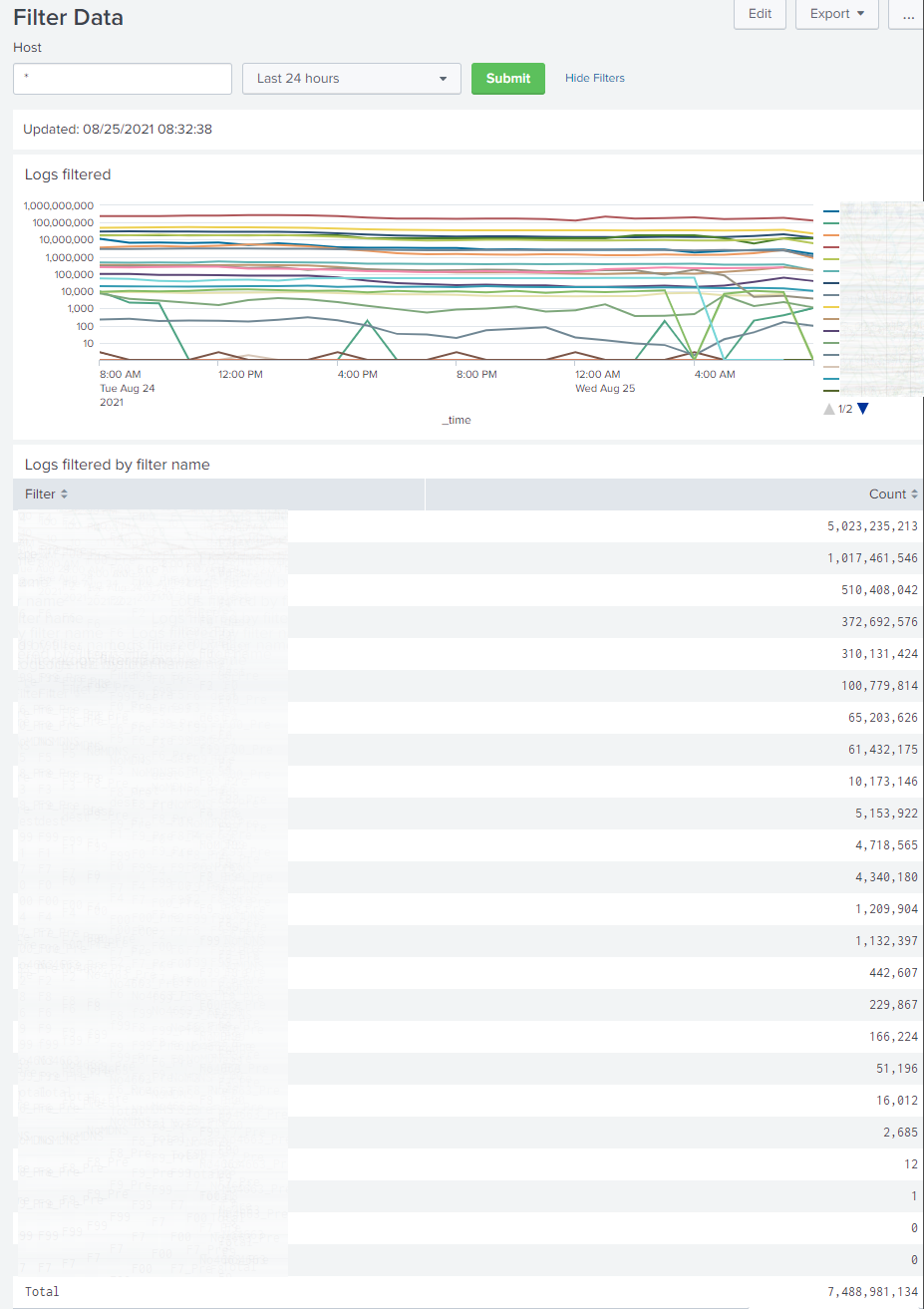
Filters
- Added filter groups to ease management of related filters
LogFormats
- Added MACHINEGUID field
- For use as a unique identifier such as a Splunk HEC channel
- Added “unix” date format
- Useful for JSON logs with Splunk HEC
Logging
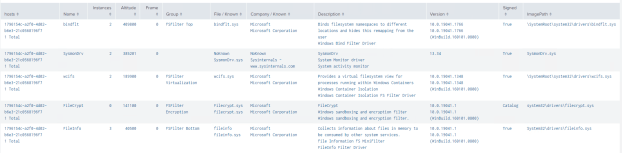
- Added file system minifilter logging
- Added LogUserChange parameter
- Log when the user changes from parent to child process
LogRouting
- Added support for HTTP servers, including custom headers
- Added parameters to verify connections meet requirements
- Useful when using HTTPS destinations and captive portals or other MITM scenarios are encountered
RemoteConfiguration
- Added parameters to support more destinations and formats
- Useful when loading remote configuration from version control systems such as gitlab and other non-standard HTTP(s) sources
- Added sysmon configuration loading
- The last sysmon configuration found when processing applicable rules will be applied
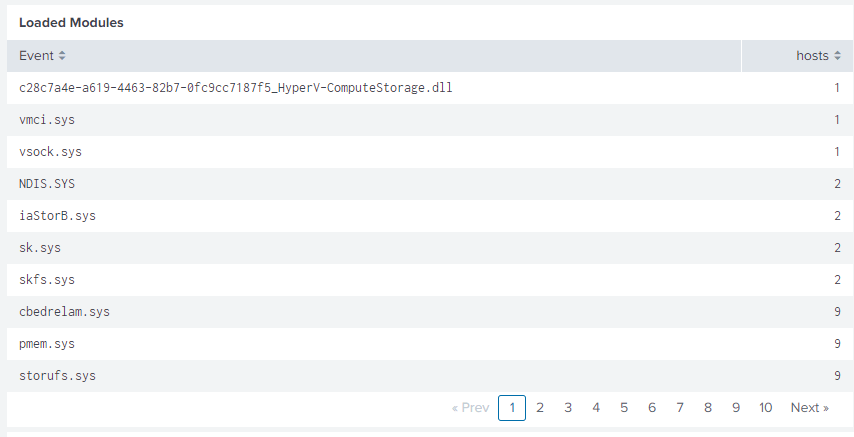
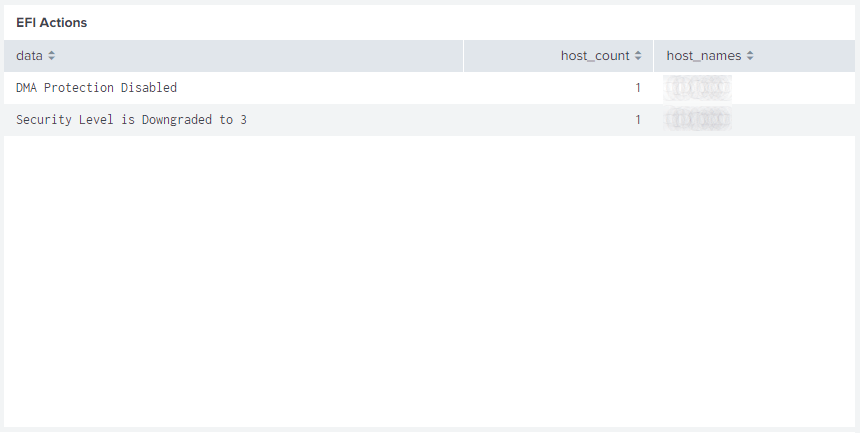
Windows Boot Configuration Log (WBCL) – New!
- Initial and periodic reporting of the WBCL
If you’d like licensing or other information about WLS, send me a note via the contact form. WLS is currently available to US entities, but does require a signed license agreement.