When reviewing event logs in Event Viewer, the General tab shows event details in a human readable format, including displaying localized strings.

However, when viewing the log on the Details tab in Friendly or XML view some of this “decoding” is not performed.


The Problem
WLS uses the XML version of logs, so these same codes were passed along instead of the localized string. For many logs this was OK since it was fairly easy to find the code in question and the corresponding value. While exploring this further (at customer request), I found that for some logs these values can change by host and version of the software generating the logs, as it is dependent on the provided message files. This made my previous plan to use static lookup tables unfeasible.
The Solution
The files that contain localized event log messages are identified for each event source in the registry at HKLM\SYSTEM\CurrentControlSet\services\eventlog\$logname$\$channel$. For example, Security log message files are identified at:
HKLM\SYSTEM\CurrentControlSet\services\eventlog\Security\Security

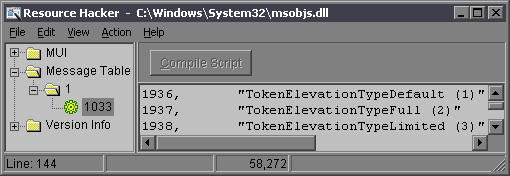
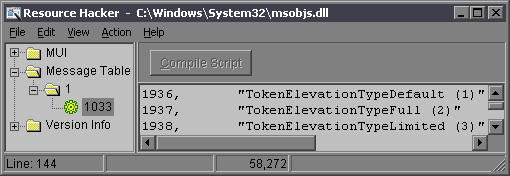
If you open the file identified as the ParameterMessageFile in a resource viewer you’ll see a message table for each language code with a list of messaged IDs and values.
Now that we have the message IDs and the file to decode them, decoding them is easy with a call to FormatMessage, which expects a handle to the message file and a message ID. The message file is loaded as a data file with LoadLibraryEx and the returned handle and a message ID are passed to FormatMessage. If successful, our string buffer now contains the message.
WLS performs the above actions if DecodeProviderString is enabled. A new field will be created with the decoded value, or if ReplaceProviderString is enabled, the original field value will be replaced with the decoded value.
Example
Field added:
[host] Security: LogType="WLS", BaseFileName="audiodg.exe", Channel="Security", CompanyName="Microsoft Corporation", Computer="[host].[domain]", CreatorProcessName="svchost", EventID="4688", EventRecordID="11668699", ExecutionProcessID="4", ExecutionThreadID="56", FileDescription="Windows Audio Device Graph Isolation", FileVersion="6.1.7600.16385 (win7_rtm.090713-1255)", InternalName="audioadg.exe", Keywords="0x8020000000000000", Language="English (United States)", Length="126464", Level="0", MD5="D5CCA1453B98A5801E6D5FF0FF89DC6C", NewProcessId="0x3188", NewProcessName="C:\Windows\System32\audiodg.exe", Opcode="0", ProcessId="0x214", ProductVersion="6.1.7600.16385", ProviderGuid="{54849625-5478-4994-A5BA-3E3B0328C30D}", ProviderName="Microsoft-Windows-Security-Auditing", SHA1="F033FD30AACD0183BFC30861891A92B56AC2468B", Signed="Catalog", SubjectDomainName="NT AUTHORITY", SubjectLogonId="0x3e5", SubjectUserName="LOCAL SERVICE", SubjectUserSid="S-1-5-19", Task="13312", TokenElevationType="%%1936", TokenElevationTypeValue="TokenElevationTypeDefault (1)", ValidSignatureDate="False", Version="0", Zone="0"
Value replaced:
[host] Security: LogType="WLS", BaseFileName="audiodg.exe", Channel="Security", CompanyName="Microsoft Corporation", Computer="[host].[domain]", CreatorProcessName="svchost", EventID="4688", EventRecordID="11668699", ExecutionProcessID="4", ExecutionThreadID="56", FileDescription="Windows Audio Device Graph Isolation", FileVersion="6.1.7600.16385 (win7_rtm.090713-1255)", InternalName="audioadg.exe", Keywords="0x8020000000000000", Language="English (United States)", Length="126464", Level="0", MD5="D5CCA1453B98A5801E6D5FF0FF89DC6C", NewProcessId="0x3188", NewProcessName="C:\Windows\System32\audiodg.exe", Opcode="0", ProcessId="0x214", ProductVersion="6.1.7600.16385", ProviderGuid="{54849625-5478-4994-A5BA-3E3B0328C30D}", ProviderName="Microsoft-Windows-Security-Auditing", SHA1="F033FD30AACD0183BFC30861891A92B56AC2468B", Signed="Catalog", SubjectDomainName="NT AUTHORITY", SubjectLogonId="0x3e5", SubjectUserName="LOCAL SERVICE", SubjectUserSid="S-1-5-19", Task="13312", TokenElevationType="TokenElevationTypeDefault (1)", ValidSignatureDate="False", Version="0", Zone="0"
For more information on WLS, click “WLS Information” at the top, or here: WLS Information
If you’d like additional information about WLS, send me a note via the contact form. WLS is currently available to US entities, but does require a signed license agreement.