Building on the existing reporting of the TPM status and certificates, WLS now has the ability to report the Windows Boot Configuration Log, also known as the Trusted Computing Group (TCG) measured boot logs. This is the same information used to perform Device Health Attestation (DHA) and that is logged at %windir%\Logs\MeasuredBoot\.
WLS reads this information directly via the API and reports it in the order provided by the OS. Known values are decoded where applicable, others are reported in hexadecimal up to the user specified byte count for later analysis. By default, reporting is enabled for the Current Static Root Trust of Measurement (SRTM), reporting for the Boot, Current, or Resume, SRTM or Dynamic Root Trust of Measurement (DRTM) is also available. These can be logged on startup and at a chosen interval to enable tracking over time of variations.
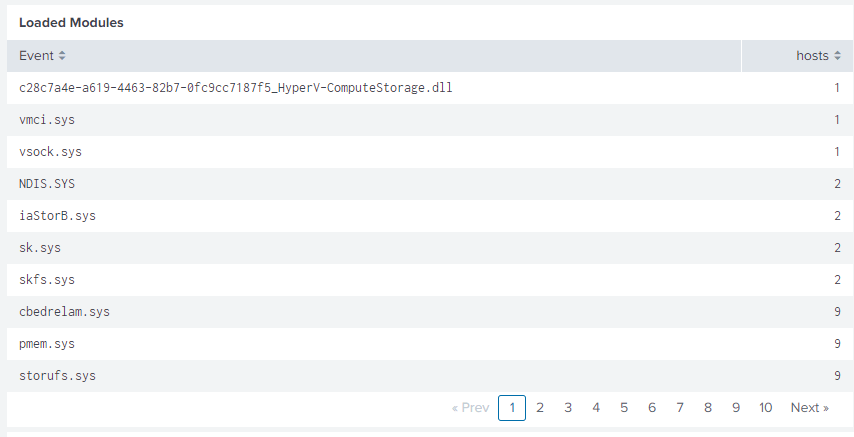
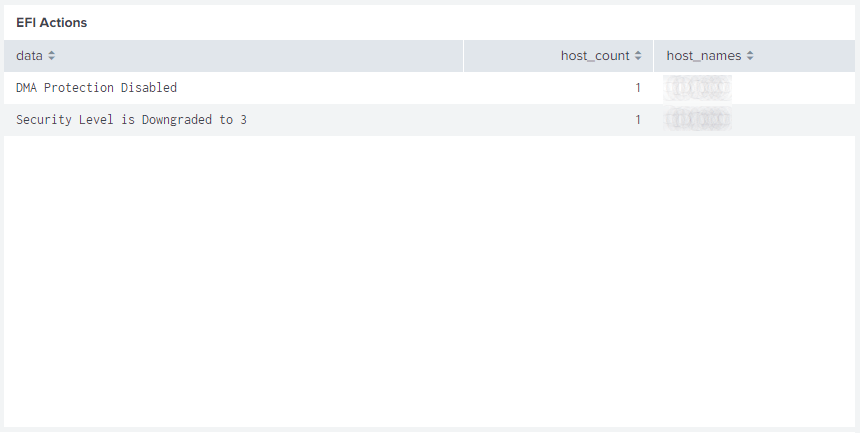
A Splunk dashboard has been created to analyze and decode these logs for comparison across all systems. This includes Early Launch Anti-Malware (ELAM), Bitlocker state and status changes, virtualization based security (VBS), loaded modules, Extensible Firmware Interface (EFI) actions, and more. Known Platform Configuration Registers (PCR) and common acronyms related to the WBCL can optionally be displayed for reference; the System Integrity Platform Attestation (SIPA) definition was surprisingly hard to find.

Rare loaded modules can help locate systems with a non-standard configuration and potentially malware.
EFI actions may show configuration issues and other important information.
The raw events are shown in-order with decoding for well-known items and hexadecimal to ascii decoding to show readable data where possible. This lets you trace one or more systems through boot process to analyze loaded modules, signing certificates, hypervisor policies, Bitlocker unlock status, and other settings.

This is just one of the new features coming with the WLS 3.7 update; others include shortcut/LNK parsing and reporting for new process events and command line parameters, loaded file system filters (fltmc), HTTP(s) log destinations, and Portable Executable (PE) directory names and values (debug, export, import, etc.).
For more information on WLS, click “WLS Information” at the top, or here: WLS Information
If you’d like licensing or other information about WLS, send me a note via the contact form. WLS is currently available to US entities, but does require a signed license agreement.